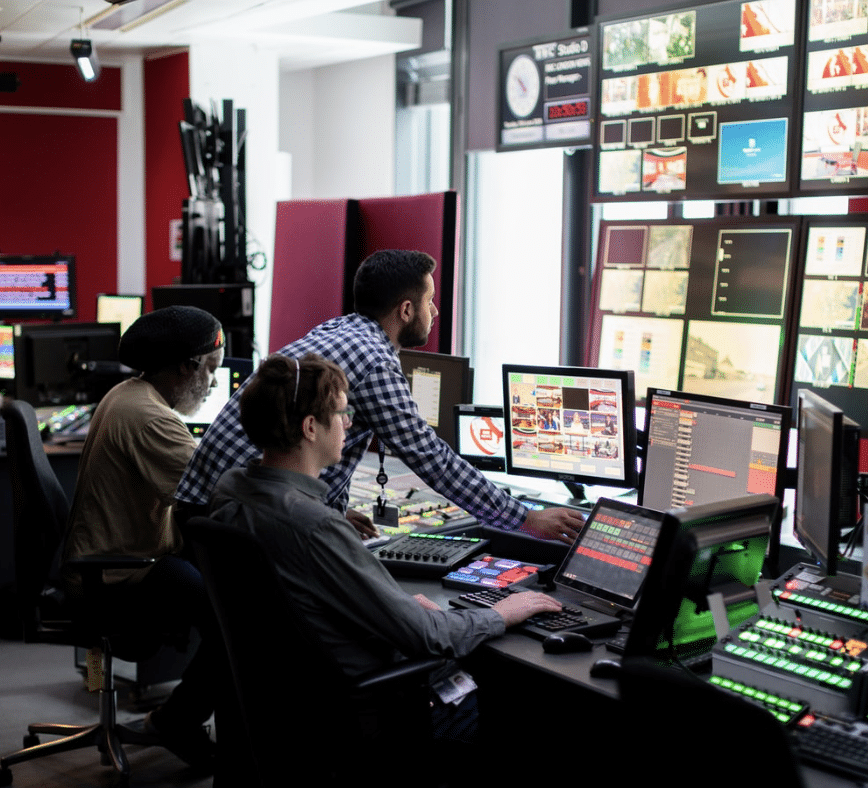
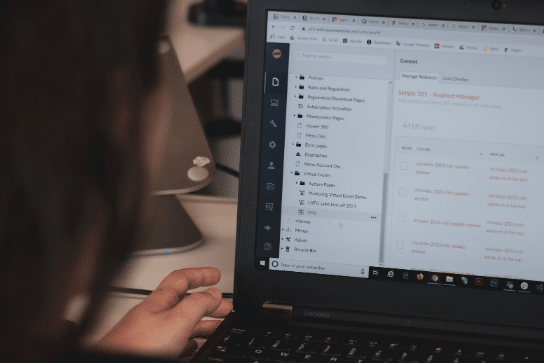
Data Security and IT Monitoring
Data security is key when working with sensitive information and large databases. While every company is at risk from data breaches to human error and security incidents, data management and monitoring are the preventive measures that can save your business.
As part of Binary Blue’s IT monitoring and data security services, we will walk you through all the data security measures you need to take, from accessing data to protecting corporate networks and monitoring personal devices for involuntary breaches.
Our cyber security team is experienced in asking the right questions to achieve the best results for your processes and database needs. We will implement the most suitable security measures for your business.

How We Help You Secure Your Data
Our approach isn’t just reactive; our highly qualified data security consultants and engineers hunt down the root cause of issues and advanced threats, ensuring they don’t re-occur. We use data monitoring tools to predict where issues might happen and fix them at the source, making your everyday life less stressful.
We constantly monitor and optimise your software, hardware and endpoint data security systems, ensuring everything is kept up-to-date and secure. Our management and security tools alert us to potential security risks and malicious software before they get in the way.
You don’t need to worry about monitoring antivirus software, data access, backups, data masking, updates or processes; we do everything for you. Our data security solutions protect data in a comprehensive and proactive manner, safeguarding it against unauthorised access, data breaches, and other threats.
With Binary Blue’s IT monitoring and data security services, you can focus on your core business activities with peace of mind, knowing that your sensitive information is in safe hands.
The Dangers We Help You Avoid
By using the latest technology in IT to resolve and prevent issues, our data security strategy will help you stay clear of various IT complications. Our services include:
- Data breach monitoring
- Data loss prevention
- Data encryption (and other data protection tools)
- Data management
- Reviewing and resolving security threats
- Data protection policies
- Data backups
- Access management
- Incident management plan
- Cloud environments
- Cloud services
- Centralised repository IT monitoring and management
Our process includes planning, research, implementation and monitoring, as well as some additional steps you may want us to look into, based on your business needs. If you want to know more about them, contact us for a more tailored definition.
Who Can Benefit from Our Service
Here are the top industries where our security monitoring services are most helpful:
Financial Services
Banks, insurance companies and investment firms, where protecting sensitive financial data is paramount to prevent fraud and comply with regulations.
Telecommunications
Companies that operate networks and services critical for communication infrastructure, where uptime is essential, and data breaches could affect millions.
E-Commerce
Online retailers and marketplace platforms that handle a large volume of personal and financial transactions are targets for cyberattacks.
Healthcare and Private Practices
Hospitals, clinics, and research labs, where patient data privacy is critical and regulated under laws like The Data Protection Act (DPA).
Legal and Court Services
Law firms and consultancy businesses that manage sensitive client information require confidentiality and data integrity.
Education
Schools, universities, and research institutions that store personal data on students and staff and conduct research projects requiring data security.
Government and Public Sector
Agencies that handle citizen data, provide public services online, and must protect against threats to national security.
Technology and Software
Companies that develop and distribute software, including cloud services, where intellectual property protection is crucial, and those undergoing digital transformations.

Why Do Businesses Need Data Security?
Protecting sensitive data—including financial data, client information, and confidential intellectual property — is one of the main reasons companies must invest in cyber security. A cyber attack that results in a data breach may have serious repercussions, such as monetary losses and harm to one’s reputation.
Your company’s activities may be disrupted by a cyberattack, leading to lost production and downtime. Making sure your business has a strong cybersecurity plan in place reduces the possibility of hackers who want to gain access to steal sensitive data, expensive disruptions and helps to preserve the continuity of your business operations.
What are Cloud Security Solutions?
A set of practices and technological tools called cloud security are intended to counteract both internal and external risks to the security of businesses. As they advance with their digital transformation strategy and integrate cloud-based tools and services into their infrastructure, organisations should consider cloud security for their computer systems and mobile devices.
Businesses that adopt these concepts and work to optimise their operational strategy face new difficulties in striking a balance between security and productivity. While more recent technologies enable businesses to expand their capabilities beyond the limitations of on-premise infrastructure, moving mostly to cloud-based systems might have unforeseen repercussions for sensitive data if not done by professionals and authorised users.
Finding the ideal balance necessitates knowing how to employ linked cloud technologies to the advantage of modern businesses while using the best cloud and network security procedures.




Managed Backup and Disaster Recovery
Our fully managed service desk will monitor your backup and disaster recovery systems, including Cloud-Based SaaS backup solutions, giving you reliable and resilient recovery options, while reducing your dependence on on-site hardware.

We will provide, install, configure and monitor an approved, industry-standard and trusted SaaS BackUp application. These back-ups are secure, and data is encrypted during the entire synchronisation, storage and replication process.
Our BackUp solution supports versioning of your backed-up data, creating a “snapshot” of the data which is saved each time. This snapshot contains all the information needed to restore your data to the exact state it was in at the time of capture.
More Services
1st and 2nd Line Support
We offer a full suite of services to support your IT instrastructure, working as an extension of your team we roll up our sleeves, take accountability and resolve the issues.
Projects and Migrations
As your IT partner, we will look at all aspects of your business and develop with you a cohesive IT strategy and cloud migration plan that supports your business goals.
Your IT Manager/ Director
As your IT partner, we will develop with you a cohesive IT & Security strategy that supports your business goals , we are an extension of your team. We want to make your IT work the way you want it.
